Lock Blog
A resource for consumers, locksmiths, and security professionals
A resource for consumers, locksmiths, and security professionals

This article is a mix of security fails that range from personal, national, and perhaps even world security. Keep in mind that this is not a list of the world’s smartest criminals, nor is it a list of the most successful. In some cases, there are no criminals at all. This list is about when security fails. Regardless of whether the parties responsible for the breaches in security were discovered, they were, in fact, able to breach the security. When your security is breached, your security has failed. As hilarious as it would be to just poke fun at these ridiculous security fails, I think it is also important to learn a lesson. Whether the failure is foreign, domestic, global, or local, there is something you can apply to your own security. We will talk about the background of the incident, the failure that is most alarming, and then extrapolate the moral of the story.

67 out of 70 times weapons and explosives were able to slip past the notice of TSA agents. Thankfully these tests were not carried out by terrorists. It was instead, Homeland Security bringing on what were simply dummy bombs and explosives. Homeland Security agents, disguised as passengers, got through with the alarming materials on their person and in bags. The materials being used to fake the weapons and explosives looked and felt like the real deal. They were correctly shaped and made of the materials that could realistically house explosives.
The screening machines, as well as the pat downs, did nothing to alert the TSA to any of the threats. In one case, an alarm was raised, but after the TSA-administered pat down, no weapons were discovered. There was a fake bomb strapped to the searched party, and the pat down was not effective enough to find it. The response from TSA has been the admission of guilt. The plan is to retrain their agents as well as test all of their equipment. This has lead to the media referring to airport security as, “security theater”. The motions of security have been performed with no real understanding, or care, for the bigger issue. It’s funny to me how stringent TSA can be about the small things, like traveling with lock picking tools, but somehow not pickup on dummy bombs and explosives.
The issue is obviously the methods being used by this agency. There are 62,000 employees, and they have an 8 billion dollar annual budget. I do not see this as a staffing problem or an issue of insufficient funding. This is a clear cut misallocation of effort and concern. If anyone has traveled by plane since terrorism became a national concern, then you know that the TSA seem to catch anyone who is not taking off their shoes or any person bringing in a water bottle. They are catching people breaking the rules. What this internal investigation has revealed is that they are simply not focusing on the correct threats.
Essentially, if you stay within the lines and secure your luggage in the right way, you will probably make it through TSA without ever being stopped (regardless of what might be in your bags). I see this tunnel vision a lot on the home security level, especially when homeowners are assessing their own security. What happens is that a residence will experience a break in or even a natural disaster. After the fallout of the disaster, the household only plans for that disaster. The focus on general security narrows to see the one weakness that has already been exploited. This is not an inherently bad thing. You do want to fix the specific issue, but not to the exclusion of every other threat.

Physical security is very important for a zoo. Unfortunately, the largest focus is often put on keeping the animals from escaping their enclosures. This fact led to the harm of a Mr. Liu at the Guilin Zoo’s Panda exhibit. During the normal daylight hours of operation, the 20-year-old student scaled the fence to the panda cage. The height of the fence was about six and a half feet. That was the only boundary between him and Yang Yang (the panda). Once that hurdle was concurred the young man found himself confronted with a very large and deadly animal. Before the zookeepers could get the man out of the cage he sustained bites on his arms and legs.
This problem stems from unbalanced protections. A 6.5 feet fence might be fine for keeping a dog locked up, but that dog’s presence is the extra level of protection that makes up for the fence’s height. The panda getting out was the only thing considered for this security. In case you are wonder why this man broke in to see the panda, it was because (in his words), “Yang Yang was so cute and I just wanted to cuddle him”.
When it comes to security you must always consider the risks. In the case of the Qixing Park zoo, they considered the risk to the visitors if the Panda got out, but not the risk to visitors if someone got in. It could be said that this is not really much of an oversight, but I would disagree. In order to have the best security possible, you have to think about people using, and even misusing the security. Essentially, people have to care enough about security in order to make sure it is effective.
Getting to the root of the desired outcome for your security is the first step. What is the purpose of the fence? In this case, it is to keep the panda in its enclosure. Why do you want to keep the panda locked away from people? To protect the people and the panda. So it would be sensible to make it more difficult for humans to endanger themselves and the animals. The issue was that the fence was only created as a boundary for the animal, not as a protective measure for its safety against intruders. The reason for this oversight is a common one. Security is ignored because it is valued less than the importance of patrons being able to be close to the animal. When security interferes with revenue, it is often security that will be discarded.

It is really difficult to find information about this particular security fail. That is because of how big and ultimately crazy this breach was. Former director of the CIA, James Woolsey, once shared the story of a nice man from China that had a few questions about our grid system. PJM contacted the state department, who were under the impression that our Chinese foreign relations relied on letting this gentleman have access to all of the grid information. After a few months, people farther up the chain of command in the federal government discovered this, and they wanted some more information.
When they got the man on the phone, he spoke very good English “Chinese intelligence officers often do” (Woolsey). The man said he was almost done with his work, and he was invited to share what he had found as kind of a debrief. The plan was to talk in two days. He left for Beijing the next day. He was never seen again. Still to this day, we do not know how skilled he was in understanding the information, what information he got, or even exactly who he worked for. To all of these questions, Woolsey has stated, “We don’t know, we will never know.”
This is one of the best examples of how a bureaucratic chain of command can cripple security. Someone at the state department obviously was doing their job, which included maintaining a friendship with China. However, they were unaware of the potential threat this added to the US grid system. The flaw is that when PJM called the state department, someone in the bureaucratic procession forwarded them to someone who did not understand the issue. The worst thing to do in this situation is to treat one individual as the sole responsible party. No one saw what was wrong, so that means that the process of requesting permission was flawed.
The only person that PJM should contact about the grid is a person with extensive knowledge on the grid. Make sure that your chain of command is not only clear but effective. You do not simply want a chain of command that is clear. If I know I need to contact the head of foreign relations in the situation where a Chinese man is requesting access, then that is what I will do. But is that the person I should be contacting? (Note: this is an example and I am uncertain who was contacted in the actual case). The parties that are contacted about issues should be appropriately informed on the matters they are addressing.

Not much is known about the Baghdad bank robbery. What we do know is that the amount stolen was more than a quarter of a billion dollars in cash. Some of the other facts we know definitely put it as one of the most outrageous security fails of all time. Somewhere between two of three bank guards conspired to make off with some of the cash lying around their office. Oddly, the number of thieves is not confirmed. What is confirmed is that all of the money was in US dollars and not in Iraqi currency (dinars).
I am sure you may be able to speculate how all of that American money made it into an Iraqi bank. It might have something to do with the past half a century of foreign policy, maybe it is unrelated. These guards were on the night shift for the Dar Es Salaam Bank, where they were apparently left alone with the cash. How they moved the money is also unknown. Without help, it is unclear how the money could have been moved through guarded checkpoints. Also considering that his money was in cash, it would have been quite heavy. Assuming that all bills were all worth $100 (largest bill), there would have been 282,000 bills. The average weight of a bill is around 1 gram, the haul would have weighed at least 622 pounds.
This comes down both a procedural issue and a hiring issue. Mix unsupervised bank vault sleepovers with untrustworthy employees and you get a bill for around $282,000,000. So how can we learn from this? Well the most important thing that concerns me is the average annual income in Iraq. That is about $4,000 a year. Assuming that there were, in fact, three robbers and not two. An even cut would have yielded $94,000,000 a piece. In order to make that much money, these men would have needed to work a total of 23,500 years. If you are not seeing the lesson yet, I will spell it out. By keeping valuables things in the reach of people that can never hope to earn them, you increase your risk for theft immeasurably.
A disparity of 23,500 years is most certainly worth the risk of life in prison, or a death sentence, for most people. In Iraq, the average life expectancy is around 70 years. That makes this score worth about 336 lifetimes. That is going to be an enticing risk for most people. A better life than you could hope to earn in 300 lifetimes! What increased the vulnerability for the bank was their hiring and security policies. The threat was increased by such a large sum of money being attended to by such a poor population of people. I doubt that most people in that area would have given up a chance at that money. Keep in mind your surrounding population, as well as your physical and procedural security.
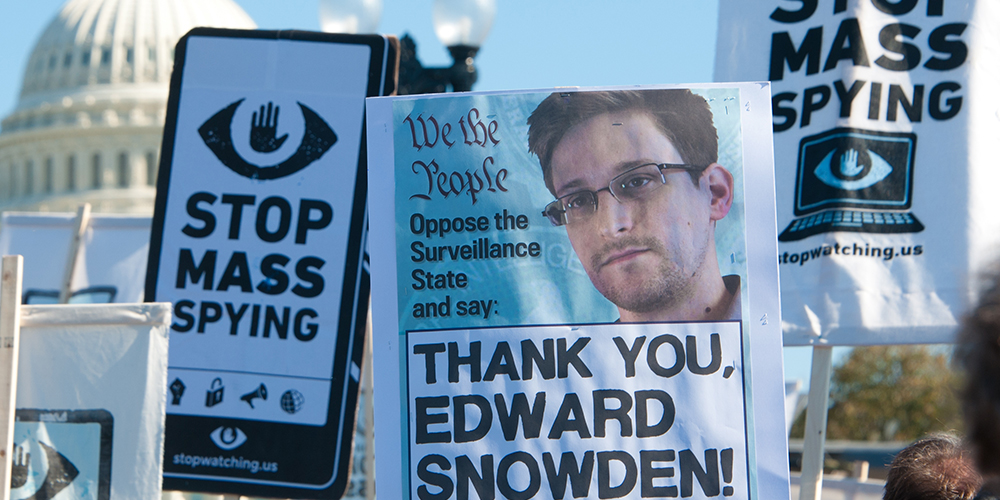
This is probably the biggest security fail of this generation. Regardless of your beliefs of whether Snowden is a traitor or patriot, the security that was supposed to keep secrets secure, failed. How did this happen? Many people point to the red flag that he did not graduate high school. I believe this is an easy distraction from a much larger failing in procedural security. Snowden had received his GED, and based on his ability to get the information he did, I would say that he had the proper knowledge needed to work as a security specialist.
If you understand security enough to defeat it, then you understand security. Skill and knowledge qualifications are irrelevant in this instance. His resume included Dell and even the CIA before he got the NSA job. This breach is about the threat of righteousness. Because what the organization was doing was unknown to the general public, but involved them, Snowden is not clearly guilty of a crime (at least in the court of public opinion). If someone acts in a morally gray way, it is much easier to justify acting against them. Justification is instrumental in gaining the help from powerful people. The biggest fail in security was the NSA not protecting themselves from being shamed for their actions.
This is a very big picture issue, but it can most certainly be applied on a micro scale. Society runs on the relationships of individuals. Think of the people that would stand by your side if you get into a fight. There is a group that will stand by you even if you are wrong, but in order to keep you safe, that group would need to be stronger than the group that believes you are wrong. Essentially you need more friends than enemies. Because our personal circles are too small to give us wide scale friendship, it is almost more important to not be hated than it is to be liked. The more enemies you have, the higher chance you have of being victimized.
Along with your risk increasing, it will be harder to narrow down the enemy who has wronged you. A good way to keep allies on your side is to not act against the general morality of your society. Do not stand out. No one comes to the aid of the meth dealer. Even if the majority of people would not harm you or your property, not being liked will decrease your chances for aid. This aid could be in pursuing legal action, catching the criminal, or even stopping them in the act. In the case of Edward Snowden, he received help on the grounds of defeating an evil, which in a way increased his own security. Take a page from Snowden’s security net.

This is a classic case of personal security. When the 41-year-old, female officer was on her way down to a parking garage, she was assaulted and robbed. At this time, the 10 year veteran of the NYPD was off duty and carrying her service weapon in her purse. The robbery took place as soon as the officer stepped out of the elevator, and should have ended as quickly as it began. Unfortunately, she was caught by surprise and fought the assailant for her purse. She did however try and retrieve the gun, at which point she was punched in the face several times. The young man, believed to be in his teens or early twenties, got control of the gun and ran off with it. The officer’s decision to carry her weapon in a bag goes against police policy.
The proper place to carry your weapon is, “an appropriate holster specifically designed to afford maximum protection against loss of weapon.” The manual even warns against carrying, “firearms in briefcases, handbags, fanny packs, hip packs, tote bags, knapsacks, paper bags or similar devices.” This violation of the rules put the officer at risk, as well as the potential victims of anyone that uses her weapon. This example can be applied to home security in many ways. If you know that an act is making your home more susceptible to break-ins and burglary, you should no longer do it. It should not take getting assaulted and robbed to highlight your mistake.
The largest takeaway is that no one is immune from the threat of physical violence. To me, this is such a large security fail because it shows that the members of society we trust to protect us, can not always protect themselves. Everyone is human. Being able to carry a gun on your person does not make you safer if you ignore key aspects of personal carry. This is also a wake-up call for self-defense training. In my experience, this is the type of thing that happens to a lot of people that get training. They practice it in the safety of a classroom, but they do not practice enough to get the muscle memory needed to overcome instincts of fear.
If you do not follow guidelines that exist to keep you safe, then you put yourself at greater risk. Had this officer been better trained in physical combat, chances are this could have been avoided. Another misstep was that by putting her gun in the bag, she was both worried about losing the weapon and not being able to get to it. In the adrenaline rush of the situation fear of the mistakes you have made can kick in. By making these large mistakes, you flood your mind with more information than you need to be processing. Ideally, you want training to kick in as a reflex.

In this instance, the main fail in security was not informing the public of the issue. As 2015 was making way for 2016, Cologne Germany was experiencing an immense influx of sexual assaults. A brash of sexual violence flooded the festivities on New Years Eve into New Years Day. The latest numbers count over 600 victims who reported their attack from that night. In spite of this tremendous risk to the public’s well-being, it took the news FOUR DAYS to cover the story. The police had even reported that the New Year’s festivals had been “relaxed”. Public media coverage of the events decried most news outlets as “liar’s press”.
The reason for the halt in information, lies, and slander of people reporting the facts was purely political. The reports detailed the assailants as “mainly migrants of north African or Arab origin”. Germany’s Chancellor, Angela Merkel, had been saying on that very New Year’s Eve that the 1.1 million immigrants respected German traditions and that those that saw them as a threat had “coldness or even hatred in their hearts” (Merkel). I am not here to talk about immigration. The failing I see is that the government’s refusal to appear wrong potentially endangered the city of Cologne. This cover-up, and conspiracy of silence, betrayed the very people these institutions were supposed to protect.
Ego does not matter if it compromises security, it is important to meet anything that compromises security head on. This is very important. When you or the people you care about are endangered, it is not about being right. It is about being safe. While you are responding to an incident, it does not matter who caused the incident. I believe that blame is not helpful at all, but if fingers are going to be pointed, this should be done after security is reestablished.
What is truly unforgivable is to make people suffer for your mistakes when you have the ability to remedy them. You should also take note of who you are responsible for. In an office setting, you may be responsible for the safety of your staff members. If you are a captain you are responsible for your passengers and your crew. If you are a parent you are responsible for your children, and it is important to make sure they do not compromise security. And if you are in public service then you serve the public. Find out who is relying on you, and do what you can to protect them.
There you have it. 7 tremendous oversights in security. We learned about everything from personal gun safety to zoo security concerns. We found that it is just as dangerous to tell the wrong people about a situation as it is to tell no one. After this list, there may be some debate as to what fail was the worst. I think that the question strays too far from the point of security. The worst failure is not that your security failed. The worst fail that can ever happen is to change nothing after it has failed. That is the real lesson of this article. Use the stories you hear in your daily life as a wake-up call to potential threats. Analyze your own vulnerabilities against the vulnerabilities of past victims. However, it is also important to remember that fear and anxiety about everything around you can be as crippling as no fear at all. Find the balance in your life. Keep your protections practical and effective. Be safe, and hopefully, we won’t see your name on the updated list.
Category: Safety & Security